Log Formatters in C# 🔗
Good description of the standard log formatters in .Net, and how to configure them.
Cancelling cancellation tokens 🔗
He's suggesting a way to inject the cancellation token into a scoped context, rather than passing it through the chain of method calls. Interesting idea, but seems a bit error-prone to me.
What is Locking and How to Use a Locking Mechanism in C# 🔗
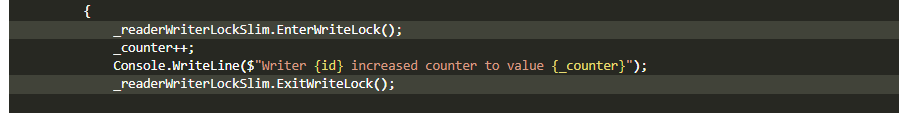
Describes all the locking mechanisms in .Net:
Interlockedclass - lock a single variablelockstatement - exclusively executes a code block with a lock on an objectMonitorclass -lockis syntactic sugar for theMonitorclassMutexclass is similar tolockandMonitor, but it also locks external threads, eg another instance of our programSpinLockclass is similar tolockandMonitor, but it doesn't block the thread - instead it spins in a loop, aka busy waiting
All of the above are exclusive locks. Below are the non-exclusive locking mechanisms:
Semaphoreclass limits the number of threads accessing a limited pool of resourcesSemaphoreSlimclass -Semaphorecan also lock external threads, whereasSemaphoreSlimis a lightweight version for internal threads onlyReaderWriterLockSlimclass has a read lock and a write lock - as you'd expect, multiple threads can acquire the read lock, but only one thread can acquire the write lock
Azure DevOps Pipelines: Practices for Scaling Templates 🔗
Best practices for organizing pipeline yaml files:
- one repository
- template scope
- file structure
- naming conventions
- conditions vs expressions
- running jobs in parallel
- variable scoping
- dependencies
- decorators
Onboard AI 🔗
The idea is nice, but I'm an AI skeptic. You point it at a GitHub repo and use ChatGPT to ask questions about it.
On Moq and our Part in the OSS Sustainability Social Contract 🔗
An opinion on the Moq fiasco.
CSS Selectors: A Visual Guide 🔗
It is what is says - a visual guide to the most popular CSS selectors - elements, classes, descendents, siblings, attributes, pseudo, etc.
The "Weak Event" Pattern in C# 🔗
Describes the problem with the event pattern - the publisher keeps a strong reference to the subscriber, so if the subscriber forgets to unsubscribe it'll prevent the subscriber from being garbage collected. This is only a problem when you have short-lived subscribers.
The solution he proposes is to use the WeakReference class. This class was designed for this purpose - allow garbage collection when this is the only reference to a class.
As well as being a solution to this problem, this sounds like a good thing to consider more often.
BearerToken: The new Authentication handler in .NET 8 🔗
I must admit I didn't quite understand the value proposition, but that's because auth is hard and I didn't really feel like blowing my mind trying to understand it. Anyway, I'll keep this link in case I need to later.
OWASP Top 10 API Security Risks – 2023 🔗
- Broken Object Level Authorization
- Broken Authentication Authentication
- Broken Object Property Level Authorization
- Unrestricted Resource Consumption
- Broken Function Level Authorization
- Unrestricted Access to Sensitive Business Flows
- Server Side Request Forgery
- Security Misconfiguration
- Improper Inventory Management
- Unsafe Consumption of APIs